|
The Ultimate Cyber Security and Risk Management Masterclass
Genre: eLearning | MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English | Size: 327 MB | Duration: 1h 9m
Become thorough with the largest domain in Cyber Security – Security and Risk Management.
What you'll learn
Understanding Vulnerability and Threat
Security governance and compliance
Legal and regulatory issues
Personnel security policies
Risk management
Description
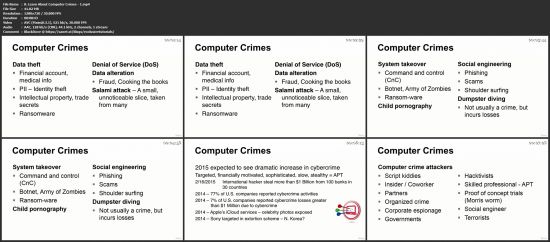
Now organizations are faced with attackers who want to steal businesses’ customer data to carry out identity theft and banking fraud. Company secrets are commonly being stolen by internal and external entities for economic espionage purposes. Systems are being hijacked and used within botnets to attack other organizations or to spread spam. Company funds are being secretly siphoned off through complex and hard-to-identify digital methods, commonly by organized criminal rings in different countries. And organizations that find themselves in the crosshairs of attackers may come under constant attack that brings their systems and websites offline for hours or days. Companies are required to practice a wide range of security disciplines today to keep their market share, protect their customers and bottom line, stay out of jail, and still sell their widgets.
This course teaches you the tools and techniques required to prevent, detect, contain, correct, and recover from security breaches and other information assurance failures. This course explains how to integrate information assurance into your enterprise planning in a non-technical manner. It leads you through building an IT strategy and offers an organizational approach to identifying, implementing, and controlling information assurance initiatives for small businesses and global enterprises alike.
In the course, we will cover many of the disciplines that are necessary for organizations to practice security in a holistic manner. Each organization must develop an enterprise wide security program that consists of technologies, procedures, and processes covered throughout this course. As you go along in your security career, you will find that most organizations have some pieces to the puzzle of an “enterprise-wide security program” in place, but not all of them. And almost every organization struggles with the best way to assess the risks it faces and how to allocate funds and resources properly to mitigate those risks. Many of the security programs in place today can be thought of as lopsided or lumpy. The security programs excel within the disciplines that the team is most familiar with, and the other disciplines are found lacking. It is your responsibility to become as well rounded in security as possible so that you can identify these deficiencies in security programs and help improve upon them. We will begin with the foundational pieces of security and build upon them through the course. Building your knowledge base is similar to building a house: without a solid foundation, it will be weak, unpredictable, and fail in the most critical of moments. Our goal is to make sure you have solid and deep roots of understanding so that you can not only protect yourself against many of the threats we face today, but also protect the commercial and government organizations who depend upon you and your skill set. |
|
udp://tracker.torrent.eu.org:451/announce udp://tracker.tiny-vps.com:6969/announce http://tracker.foreverpirates.co:80/announce udp://tracker.cyberia.is:6969/announce udp://exodus.desync.com:6969/announce udp://explodie.org:6969/announce udp://tracker.opentrackr.org:1337/announce udp://9.rarbg.to:2780/announce udp://tracker.internetwarriors.net:1337/announce udp://ipv4.tracker.harry.lu:80/announce udp://open.stealth.si:80/announce udp://9.rarbg.to:2900/announce udp://9.rarbg.me:2720/announce udp://opentor.org:2710/announce |

